Single RCE Vulnerability that affects Microsoft, Yahoo and Orange
Ebrahim Hegazy, a Bug Bounty Hunter from Egypt, has identified a security vulnerability that allowed him to hack Microsoft, Yahoo and Orange.
Ebrahim Hegazy, a Bug Bounty Hunter from Egypt, has identified a security vulnerability that allowed him to hack Microsoft, Yahoo and Orange.
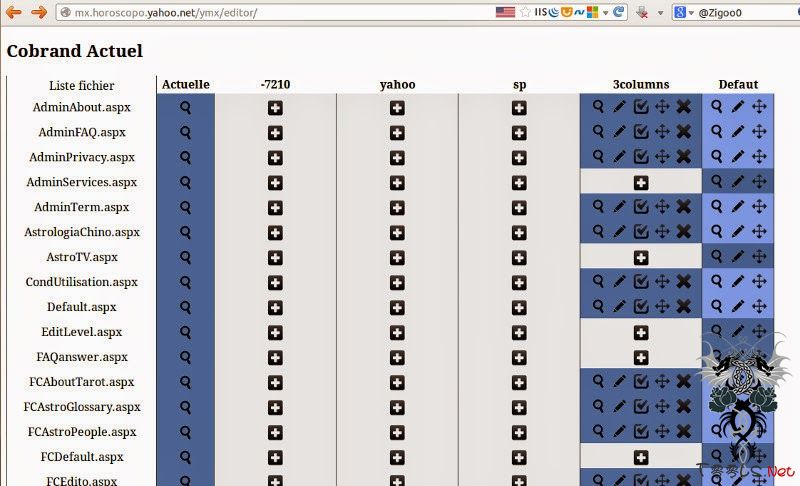
While he is on the hunt for a security bug in Yahoo domains, he found a web page that allowed him to upload .aspx file and modify the existing aspx files.
You can just create a new file by sending POST request to the URL " http://mx.horoscopo.yahoo.net/ymx/editor/inc/GenerateFile.aspx" with the following post content: "FileName=New_File_Name.aspx&FileContent=File_Content_Here".
Ebrahim has simply uploaded a file called 'zigoo.aspx' with 'zigoo' as content. To find out other Yahoo domains that were affected by the same vulnerability, researcher did a Bing search.
The following domains were also affected by this bug: **.horoscopo.yahoo.net, astrocentro.latino.msn.com, horoscopo.es.msn.com, astrologia.latino.msn.com, horoscopos.prodigy.msn.com and astrocentro.mujer.orange.es.
Interesting fact about this vulnerability is that the page created in Yahoo domain reflected in other domains also.
"It’s A CDN(Content Delivery Network) Service for astrology that cashes the same content to render it for the sub domains of that mentioned vulnerable domains, So all files on one domain will be shown on all other domains on the server." Researcher says.
After reporting to Yahoo, Yahoo has rewarded the researcher with some bounty. As usual, Microsoft didn't give any reward to the researcher.
评论4次
这个新闻发的好刁,还有URL填的不对喔
T00ls国际化了,允许国际黑客的存在。楼主来自伊朗……
我昨天还说这么问题了,国际化好
这个新闻发的好刁,还有URL填的不对喔
T00ls国际化了,允许国际黑客的存在。楼主来自伊朗……
这个新闻发的好刁,还有URL填的不对喔
说是漏洞,还不如说是开发时候自带的后门……这不是写文件的aspx小马么?